SANS Hosted a Blockchain Security Summit
Woah, let me just say, it was incredibly nice to attend and be a part of this summit - Thank you SANS!
The blockchain space has seriously struggled to get a good reputation for the past several years due to the cyberattacks that are constantly happening on it. Truthfully, many experts feel like this is the next best step in our “technology evolution”, but the reason why things are going so horribly wrong is because we just aren’t implementing security right.
So, if you couldn’t tell already, we’ll be breaking down and scratching the surface of what was talked about at the summit/what some interesting takeaways are for you to share!
Blockchain is Different From Current Technology
Blockchain in and of itself is a totally different concept than a traditional network topography that we know - as discussed in earlier versions of this HackerHub articles.
For example, the traditional the models, frameworks, standards, and tools we all use today for cybersecurity have no impact and do not work for blockchain.
”UGH, so that means you’re telling me I have to learn a bunch of new concepts?”
Well, yes and no. While you will need to spend time getting to know these new things, the fundamental concepts of cybersecurity are the same.
In my own personal opinion - Not HackerHub’s opinion, if implemented securely, I feel that supplementing current cybersecurity standards with blockchain backends will pay off for organizations in the long run, two-fold! The only downside is that it will be quite the endeavor.
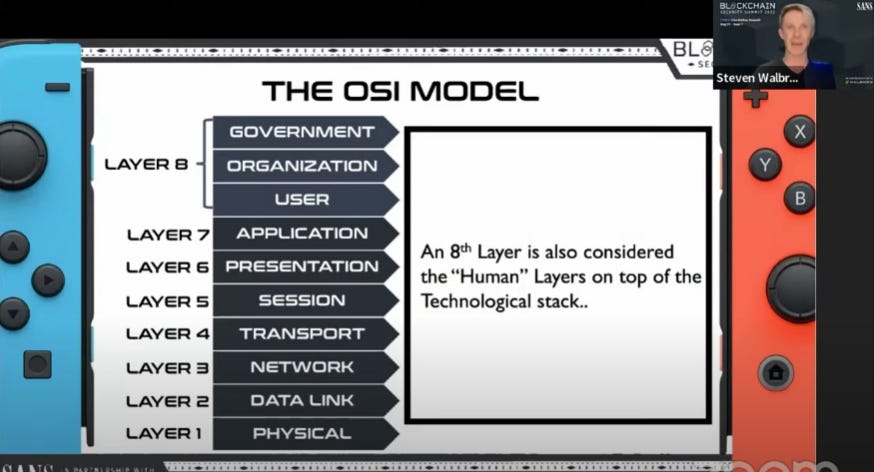
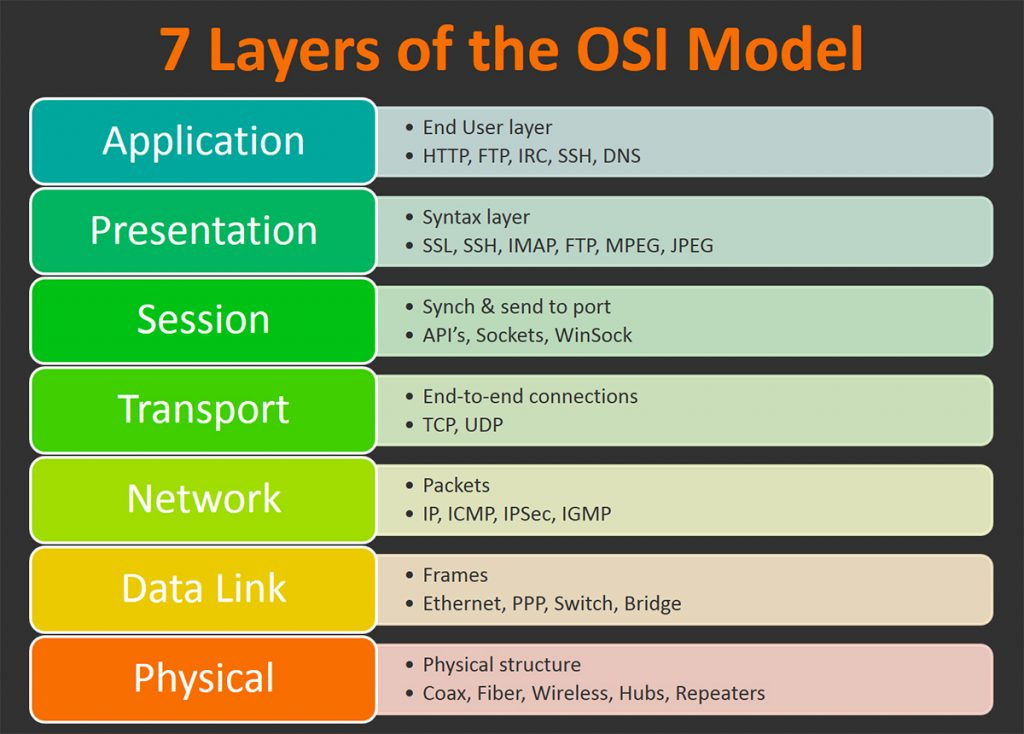
Let’s take, for example the current OSI Model:
Government
Organization
User
Presentation
Session
Transport
Network
Data Link
Physical
This is something that we all, for the most part, have at least heard about.
Now, let’s take a look at the blockchain OSI model:
Policy
DAO
User
DAPP
Scalability
State
Transaction
Consensus
Peer to Peer
Physical
Now, yes, there are some terms up there that we aren’t quite familiar with, but that’s okay! There doesn’t seen to be a fully agreed upon OSI model quite yet in the industry (things are still growing right not), so at this moment, we won’t be breaking down any of those terms above.
The general gist of how the model looks and how it works is the same though.
I’ve included two different OSI models in the pictures below:

How does this really affect us right now?
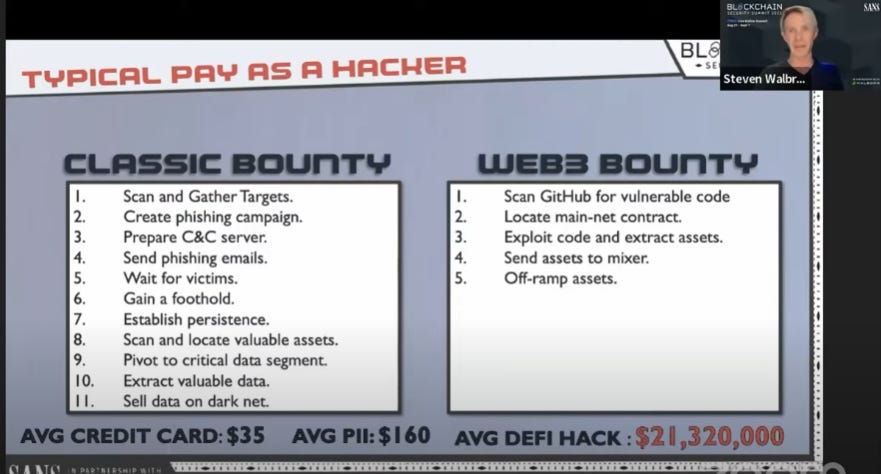
As a method of measurement, lets look at bug bounties.
“A bug bounty is a monetary reward given to ethical hackers for successfully discovering and reporting a vulnerability or bug to the application's developer. Bug bounty programs allow companies to leverage the hacker community to improve their systems’ security posture over time continuously” according to hackerone.
On average, for a Web 2.0 bug that is found for a company - if a malicious threat actor (hacker) were to steal credit cards and/or PII (Personally Identifiable Information), they’d make a return of roughly $35 and $160 for each record they compromise, respectively.
The biggest difference in Web 2.0 and Web 3.0 is that with blockchain, a bounty isn’t always just compromising a record or data… specifically with DeFi (Decentralized Finance) it’s compromising cashflow/money.
Web 2.0 bounty average pay day for a black hat hacker:
- Credit Cards: $35
- Personally Identifiable Information: $160
Web 3.0 bounty average pay day for a black hat hacker:
- Decentralized Finance Vulnerability: $21,320,000
Obviously, especially with DeFi, it’s a huge deal that an attacker can cause such a ruckus by exploiting a vulnerability on the blockchain, but more than ever, this is why we need to learn this.
Blockchain isn’t going anywhere any time soon and it’s here to stay for a while. With massive companies transferring backend systems to blockchain based systems, there’s no second guessing the immense cybersecurity need for blockchain.
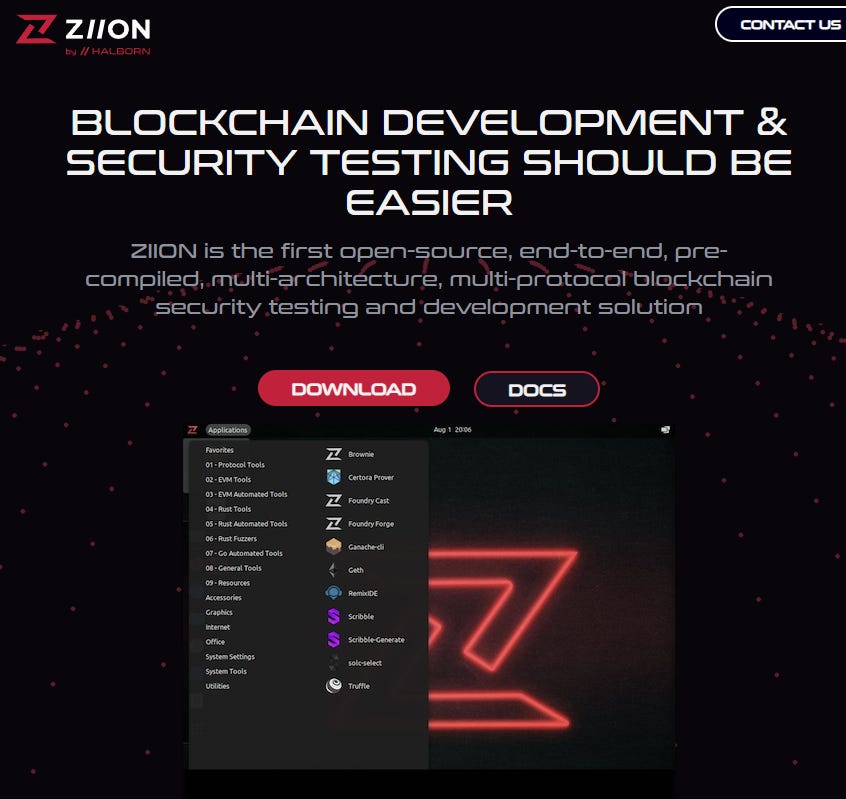
If you’d like to experiment with the Blockchain Development and Security Testing realm, check this out!
Introducing to you, ZIION!
What is ZIION?
ZIION contains over 100 tools, utilities, dependencies, and packages to immediately begin working with solidity/evm and rust-based blockchains.
What technology is ZIION built on?
With Kali Linux as a reference point, we’ve built ZIION to make blockchain security more accessible.
Who is using and building on ZIION?
Developed by blockchain security engineers, for blockchain security engineers.
If you’re wanting a little challenge to work on with ZIION, then try this out below:


Least to say, I’m incredibly excited to keep delving into this industry. There’s a whole lot to come and at a faster rate than we know.
If you’re still reading this… I applaud you *polite golf clap*. Thanks for bearing with me on this article and I hope you enjoyed it!
Until next time…
Cheers everyone,
-William
Thanks for taking the time to check out HackerHub! If you enjoyed this article and would love to have more cybersecurity wisdom delivered directly to your inbox, go ahead and hit that subscribe button!